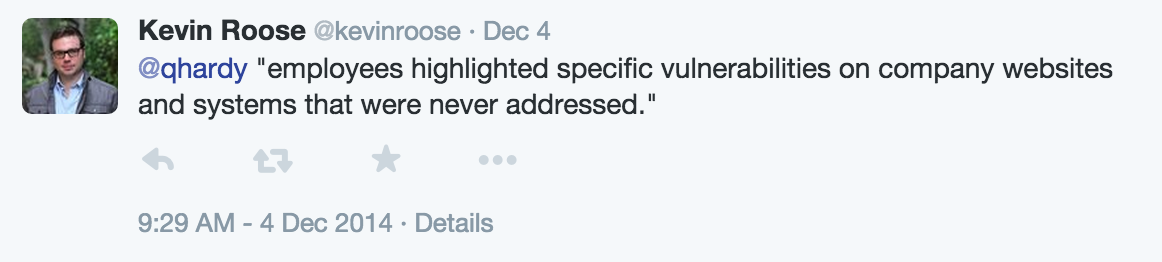
So I've been watching breaches for many years and the latest Sony breach is awe inspiring in terms of the scale of the breach and maliciousness in intent; the breach seems to transcend the typical profiteering objectives and feels more like economic espionage. The scale and intent of this breach seems to have intersected with a company which lacks both value in security management as well as IT governance. They clearly have not learned from past mistakes and now they seem to now be faced with the biggest security spectacle in a decade.
Only time will tell, but at this point this breach may have lasting impact in the minds of executive management worldwide. IT governance could rank higher, much higher, in the minds of corporate leadership. From a governance standpoint the impact of many breaches is reduced mainly to quantifiable dollars, perhaps the cumulative cost of the breach and impact to stock price with a little brand damage thrown in. Even 100 million dollars of breach cost is not nearly catastrophic for a business unit that can generate multiples of that in profit in a single quarter. However, whatever the future holds for Sony, it's not inconceivable to see a scenario where the entire Sony Pictures Entertainment crumbles and significantly impacts the greater Sony conglomerate. It's not so much that that will happen as much as that scenario seems plausible. Corporate boards will be able to visualize that in their own organizations. With that potential impact I feel that we could be ushering in a new era of IT governance.
A couple of thoughts come to mind for corporate boards and IT stewardship in terms of their ability to provide effective IT oversight.
1. Every board should be able to answer the following questions as part of a competency test for their ability to manage security risk and IT governance:
- What are the risks associated with having the security department report directly into the IT organization? and,
- Who is reporting to the board about security risk and IT controls and what might their bias be?
Hint 1: One key unstated objective of a corporate CIO or IT director is to keep their job, put food on the table and otherwise keep a paycheck; a good way to achieve that is to demonstrate what a great job they are doing, which in fact can be said about most jobs.
Hint 2: A key objective of a security assessment of an outside auditor is to identify weaknesses in the IT environment.
Hint 3: Hint 2 is in direct conflict with Hint 1.2. Does the board have a technical member that can help facilitate meaningful discussion around security and technology infrastructure.
Clearly the Sony breach demonstrates a new avenue and motivation for security breaches. From a governance perspective, the risk should be perceived as much more open-ended. Perhaps the day of classifying data disclosure purely in terms of monetary impact that can be insured against or hedged with huge profits is over. Corporate risk management will begin so imagine breach impacts so significant that it could change the course of an entire company.